- Security Operations
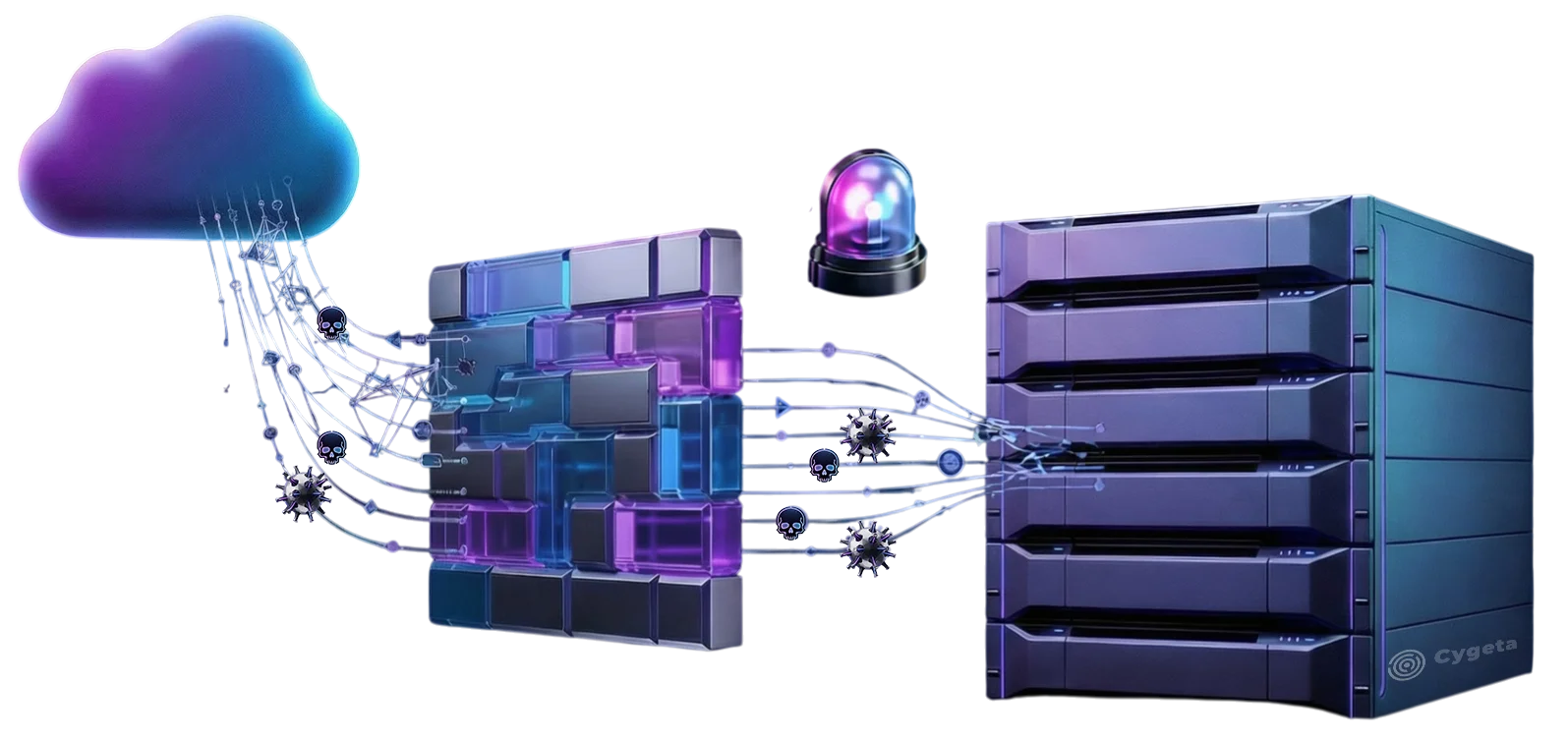
Security Control Validation
Independent verification of security control effectiveness
Optimize Spending
Gain data-driven insights to prioritize and optimize your cyber security budget and spendings
Better Choices
Make deployment, tuning, and vendor choices based on evidence from testing – not feature lists
More Confidence
Know which controls truly prevent, detect, and respond – before attackers prove the gaps
What You Get
What we validate is practical, testable, and evidence-based focused on proving control behavior under realistic conditions
Configuration & Policy Review
We perform detailed reviews of security configurations, rule sets, policies, and deployment architecture. This ensures controls are aligned with your intended risk posture rather than default or partially implemented settings
Control Effectiveness Testing
We execute controlled validation scenarios to confirm whether controls prevent, detect, or log specific attack techniques. Testing focuses on measurable outcomes and observable system behavior, not theoretical capability
Integration & Workflow Validation
We assess how tools interact across your environment, including logging, alerting, correlation, and escalation paths. This verifies that controls function as an integrated security stack rather than isolated point solutions.
Gap Identification & Remediation Guidance
We document control gaps, misconfigurations, and operational blind spots discovered during validation. Findings are prioritized with clear technical recommendations to improve coverage, tuning, and resilience.
Evidence you can act on - clarity you can defend
Reduced Uncertainty
Stop guessing whether “green dashboards” equal protection. Testing turns assumptions into measurable outcomes
Risk-Based Priorities
Gaps are mapped to impact and likelihood so remediation is practical and sequenced. All aligned to business needs and risk
Lower Operational Noise
Identify noisy detections or false positives and missing context that slow response and distract security teams
Real Coverage Insight
See what’s actually blocked, what’s merely logged, and what slips through. This supports smarter tuning and layered defense decisions
Better Vendor Outcomes
You get evidence-based conversations with vendors - clear reproduction steps, expected vs actual behavior, and verification criteria to shorten your “time-to-fix”
Safer Change Planning
Validation is designed to be low-interruption and coordinated with operations so you can test while the business keeps working
Our Process
A simple, structured approach that proves what works, exposes what doesn’t, and guides the fixes
1.
Align & Scope
We define the controls, success criteria, and what “effective” means in your environment. We also agree on safety constraints, test windows, and evidence sources
2.
Baseline & Review
We collect current configs, policies, and architecture context to understand intent and dependencies. This creates a baseline for comparing “configured” versus “operational.”
3.
Test & Validate
We run controlled tests to measure prevention, detection, and response outcomes. Where useful, we use realistic attack emulation to confirm performance without disruption
4.
Analyze & Gap Map
We document gaps, root causes, and integration failures (tool-to-tool and workflow-to-workflow). Findings are prioritized and tied to clear remediation actions
5.
Remediate & Re-Validate
We support implementation fixes, configuration changes, and tuning. We then perform targeted re-testing to confirm controls now operate as intended


